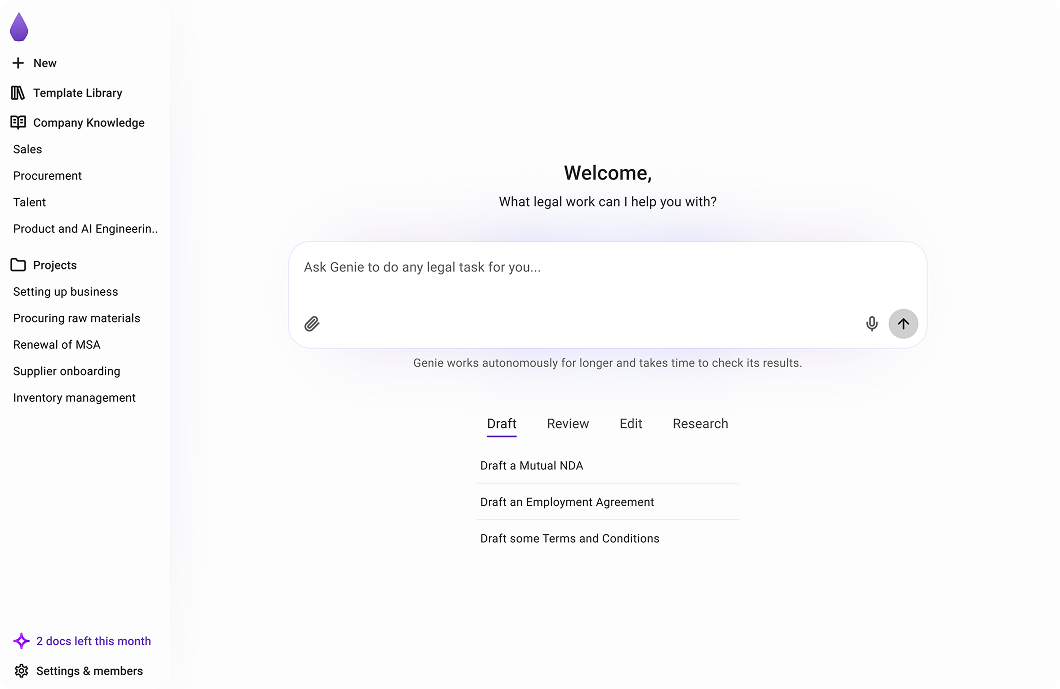
A legal brain for every business team
What legal work can I help you with?
Ask Genie to review this customer’s MSA against our playbook...
Ask Genie to review this customer’s MSA against your playbook...
Ask Genie to compare the client’s redlined MSA against our standard MSA...
Ask Genie to draft a SaaS Agreement with Acme Corp for $50K annual...



Agree With Confidence
Agree With Confidence
Launched in 2017 by founders taught by Google DeepMind. Genie's agents outperform GPT & Claude by 140%, making it the #1 platform for business teams working on complex contracts.
Based On Our Intelligence
K+
Contracts
M+
Clause revisions
+
Jurisdictions
Genie AI
The Global Legal Brain
Your context, your rules.
Our data and intelligence.
Deals closed faster with confidence.
Backed by leading investors





Watch video
Multiply your
team
speed
impact
with Genie Agents
Turn your company’s knowledge into confident decisions
Informed by your past contracts and negotiation history.

Control when you need it. Delegate when you don’t
Focus on what matters. Standard terms, handled automatically.
Agents that can handle complex, multi-document deals
From simple drafts to complex, cross-border negotiations.
Your contracts don't stop working when you sign them
Every agreement, automatically organised, monitored, and surfaced, so nothing slips through the cracks after the ink dries.
Explore more of Genie Agents
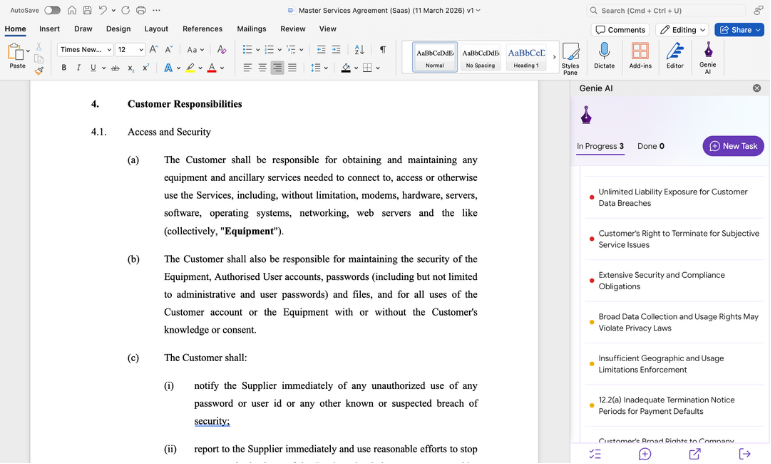
Perfect recall across every document.
Powered by Eidetic Intelligence, Genie manages complex, multi-document deals without losing a clause, figure, or cross-reference. Surface risks across your entire portfolio.
Learn more


Negotiate with AI edits in tracked changes.
Genie edits, redlines, and manages multi-party negotiations directly in tracked changes. Export as Word anytime.
Learn more


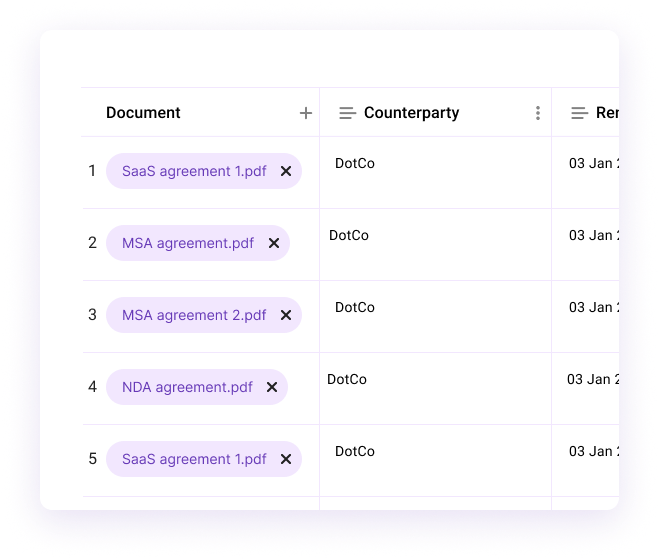
Surface tabular insights across hundreds of documents.
Extract, compare, and monitor key data points across your entire document set in a single table view.
Learn more


Fill templates automatically.
Genie fills your templates using prior answers, past deals, or reference documents. Just review and send.
Learn more


Compare multiple documents at a glance.
See what changed between versions or across documents, without scanning line by line.
Learn more


Review against your playbook.
Spot risky clauses instantly, and get suggested edits based on your standards or any precedents.
Learn more


Connect Genie to your entire stack.
MCP connectors, API, and native integrations with email, CRM, cloud storage, and eSign.
Learn more

Draft documents from scratch or using templates.
Genie guides you step-by-step through creating contracts tailored to your use case, with structure, clauses, and logic built in.
Learn more


Keep everything organised, automatically.
Templates, drafts, and signed contracts get sorted by departments. Your team always finds what they need.
Learn more


Explore all features

How is Genie different from LLMs?
Genie is built for real legal workflows inside companies.
Learn more about Genie vs LLMs

Conversational interface
Can upload docs & PDFs
Review against your playbook rules
Edit and negotiate in tracked changes
Collaborative legal editor for teams
Compare against a proprietary legal dataset
Manage complex deals with Eidetic Intelligence
Develop an org-wide legal brain
Save templates, playbooks, insights
The leading legal AI platform for businesses
Technology

Technology
Accelerate growth with watertight contracts, without slowing down your team.
Draft NDAs, MSAs, data-sharing, and partnership terms in seconds, and review contracts for risk or market standard before you sign.
Learn more

Energy

Energy
From EPCs to supply agreements.
Automate high-volume contracts with confidence.
Genie helps energy teams standardise complex terms, review risk instantly, and stay compliant across regions; without needing legal in-house.
Learn more

Construction

Construction
Cut delays from legal back-and-forth by empowering your commercial team.
From subcontractor terms to supply agreements, Genie enables fast drafting, redlining and review; tailored to NEC, JCT, and bespoke frameworks.
Learn more

Explore more industries

Security & data
Your documents stay private. Always.
Genie is built with privacy, security, and control at its core.


Moments that moved the world forward
A look at how Genie reshaped the way businesses agree.



Get started with Genie Agents today
Free
From
$0
per month

1 user
Limited AI tokens

100K tokens is enough to try
1 document in Genie.

Insights from 10 docs
Get started free


Includes:
AI Document Toolkit

AI document creation

AI document ask (Q&A)

AI document review & editing

500+ document templates

Docx editor & PDF import

Privacy-aware doc sharing
Pro
From
$75
per month

cancel any time

1 user
10x Free plan AI tokens

If you work on 5 documents a month, each roughly 50 pages, that's about 1M tokens — this plan has you covered.

Insights from 50 docs
Get started free

Includes everything in Free, plus:

Legal Brain

Multi-document transactions with agentic workflows

Eidetic Intelligence (outperforms GPT & Claude)

Store & Ask AI across unlimited documents

Extract tabular insights from up to 50 docs

Standards & Guardrails

Team playbooks & negotiation rules

Turn documents into smart forms

Business department spaces
Enterprise
From
$600
per month

Unlimited users
Unlimited AI tokens

Insights from unlimited docs
Get a quote


Includes everything in Pro, plus:

International Coverage

150+ international jurisdictions &
10+ languages

Organisational Brain

Extract tabular insights from unlimited docs

Train AI on your org’s standards & risk positions

Teach & tune AI agents with custom skills (beta program)

Auto-sync finished projects into your org's insights

Integration

SSO authentication

API & MCP integrations

Support

Dedicated CS Manager & onboarding

Bespoke AI training program

Success metrics & ROI reporting

SLA with technical support
Have questions? Find clear answers.
Everything you need to know about Genie.


Genie AI is the legal agent that builds organisational knowledge and completes work autonomously according to your rules and standards. It helps you draft, review, edit, and negotiate agreements quickly and with confidence - so you can move deals forward without waiting on lawyers or getting stuck in legal complexity.
From NDAs to commercial agreements, Genie turns legal work from a bottleneck into a fast, repeatable workflow.
Read more about Genie



Genie is fundamentally different from ChatGPT, Claude Cowork, and other general-purpose LLMs because it's not a chatbot adapted for legal work. It's a purpose-built legal AI platform powered by a patent-pending architecture called Eidetic Intelligence.
While standard large language models generate fluent text based on probability and limited context windows, Genie uses a structured, quality-gated system that maintains perfect recall across every document, clause, and financial figure. It preserves cross-document relationships through a semantic graph architecture, validates outputs at every stage, and prevents hallucinations before they impact the final result.
In simulating a real-world 65-document scenario, Genie achieved 90% legal accuracy, compared to 79.3% for Claude Cowork and 37.3% for ChatGPT. The difference isn’t just better prompting, it’s better architecture. Genie is designed for contract drafting, legal risk analysis, regulatory coverage, and board-grade decision support.
Instead of stretching a general AI into legal workflows, Genie delivers validated, evidence-backed legal intelligence built specifically for professional legal work.
Read more about Genie's performance vs LLMs



Genie is built for business teams that need to move fast on contracts, but don’t want to rely on lawyers for every decision.
It’s designed for founders, commercial teams, and operators who are constantly drafting, reviewing, and negotiating agreements as part of running the business. These are teams dealing with high volumes of customised contracts - sales agreements, partnerships, supplier deals - where speed matters, but so does getting the details right.
Rather than acting as a tool you consult occasionally, Genie becomes your organisation’s legal brain: it understands your standards, applies your rules, and carries out legal work on your behalf. As it learns from each contract and negotiation, it allows teams to operate with increasing confidence - making decisions, closing deals, and managing risk without legal becoming a bottleneck.
Explore how Genie could support your team



Genie combines autonomous execution with deep legal intelligence.
It reviews contracts against legal structures, market standards, and internal consistency, while applying your organisation’s own rules and risk thresholds. Every action it takes - whether drafting, editing, or negotiating - is guided by both legal data and your company’s preferences.
At the core of this is our patent-pending system, Eidetic Intelligence. Unlike traditional AI models that rely on limited context or one-off prompts, Eidetic Intelligence gives Genie effectively unlimited memory across documents, negotiations, and company knowledge. This allows Genie to reason across entire deal histories, cross-reference clauses, and maintain consistency not just within a document—but across your entire organisation’s legal activity.
As Genie processes more contracts, it builds a memory of how your business handles legal decisions, improving consistency and accuracy over time. This means outputs aren’t just plausible - they’re aligned with how your organisation actually operates.
Read more about Genie's perfomance



Yes, Genie is designed to operate as a trusted system for sensitive legal work.
Your documents are completely private to your organisation. We do not train our AI models on your data - Genie improves independently, so your contracts and company information remain confidential at all times.
All data is protected using ultra-secure 256-bit encryption, and we are ISO27001 certified, ensuring rigorous standards for how your information is stored and managed.
You also retain full ownership of your documents and their contents. Genie gives you complete control over your data, including who can access it within your organisation.
Because Genie becomes your organisation’s legal brain, safeguarding your data is fundamental to how the product is designed.
Read more about Genie security measures



Yes, this is core to how Genie works.
Genie operates within your organisation’s guardrails. It can use your templates, apply your preferred clauses, and follow your negotiation playbooks when drafting or reviewing contracts.
Over time, Genie goes further than just following instructions: it learns from how your team edits, negotiates, and approves agreements, building a continuously evolving legal brain that reflects your standards and decision-making. The results is legal documents delivered both faster and more reflective of the needs and preferances of your organisation.
Read the full benchmark study



You can start immediately.
There’s no complex setup required to begin using Genie, and you can try it for free. Simply upload a document or start from a template, and Genie will begin drafting, reviewing, or editing straight away.
As you use it, Genie becomes more powerful - learning your preferences and building your organisation’s legal brain in the background, without requiring heavy upfront configuration.
Try Genie now


Trusted by 200,000+ users
Drafts, reviews, and negotiates contracts autonomously.
.png)
A legal brain for every
business team
Continue with Google
Continue with Email